Data Security for Government Facilities
Your facilities organization data is a valuable asset that must be protected.

Importance of Data Security for Government Facilities
FacilityForce provides comprehensive data security solutions specifically designed for government facilities, ensuring the protection of sensitive data and compliance with stringent government regulations.
Data security is a set of processes and practices designed to protect your critical information technology (IT) ecosystem including its files, databases, and accounts from unauthorized access or corruption. Data security is critical to public sector organizations and must be integral to all stages of the data's lifecycle from inception to disposal. When ingrained within the people, the process and the organization, data security will guard against cyberattacks, human error and hardware failures.
Data security can be categorized into types including: access controls, authentication, backup & recovery, data erasure, data masking, data resiliency and encryption. There are also three core elements to data security that all organizations should adhere to: confidentiality, integrity and availability. Data security is a critical element to regulatory compliance, so you’ll want to work with an experienced software provider that takes data security seriously and partners with you on compliance.
Key Benefits
Safeguard
Valuable Data
Valuable Data
Protect Your
Reputation
Reputation
Defense Against
Hackers
Hackers
Maintain
Compliance
Compliance
Geo-Replicated
Backups
Backups
Prevent Website
Downtime
Downtime
Responsibility to
Community
Community
Avoid Costly
Recovery
Recovery
Our Unique Approach
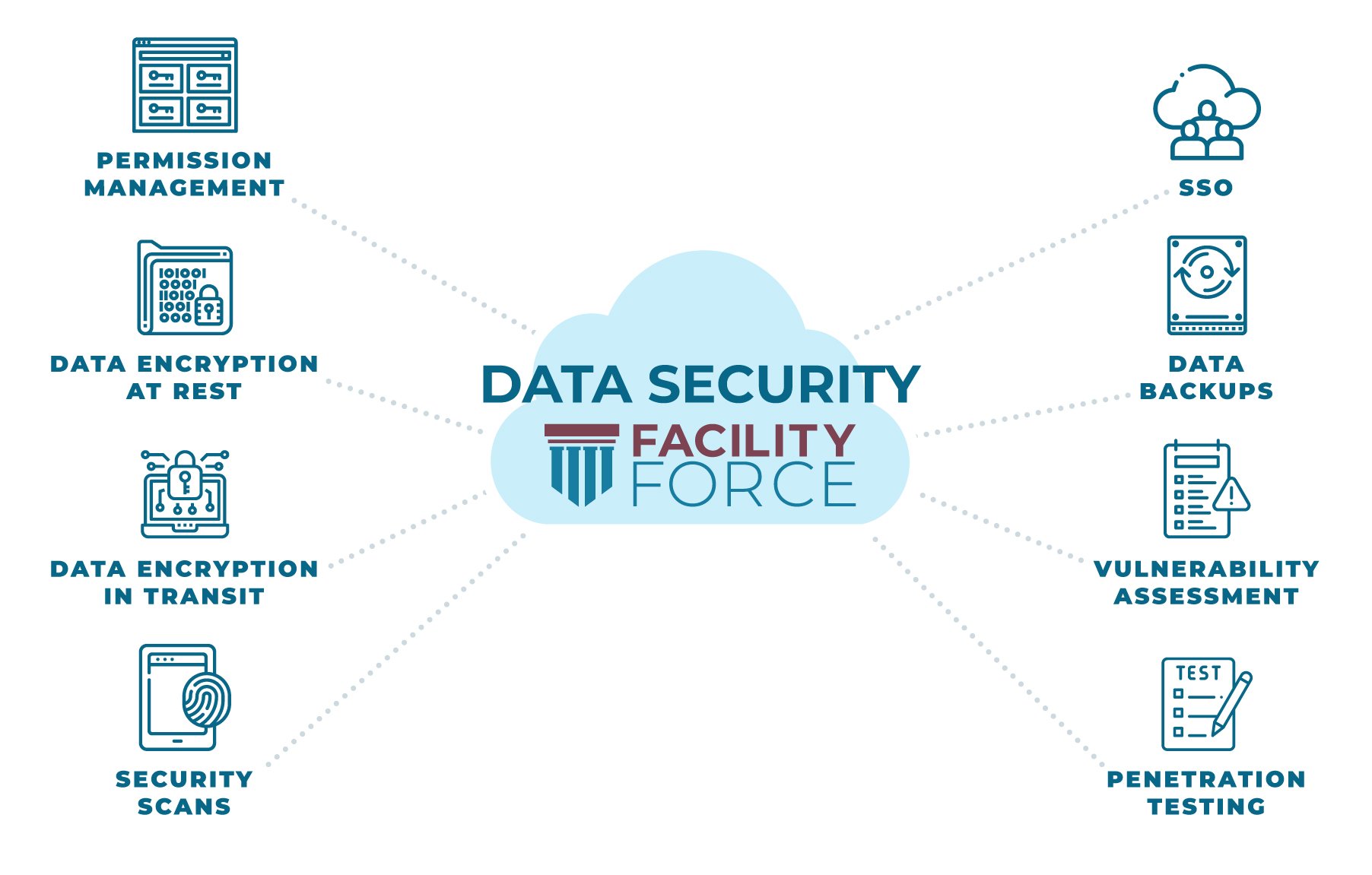
Your Data Security is a Priority
FacilityForce is committed to ensuring your data security, whether we host your system or not:
- Enjoy the benefits of Single Sign-On (SSO) including improved security compliance. We support LDAP, Shibboleth and CAS (Central Authentication Service) out-of-the-box.
- Data encryption supported by the following database platforms: Microsoft SQL Server, Oracle, and MySQL.
- Secure access to APIs for reporting and real time interfacing
- Authentication auditing
- Multiple levels of authorization based security:
- Screen and table level role based permission controls
- Row level security with SQL based security filters
- Multi-tenanted security for for separate organization managed by the same instance
- Administrator controlled queries assignable by group
- FedRAMP Compliant (see below)
- Automated continuous security scanning of all products
- Known vulnerabilities are proactively managed, and security patches are applied as required
FedRAMP Compliant
FedRAMP stands for the “Federal Risk and Authorization Management Program.” It standardizes security assessment and authorization for cloud products and services used by U.S. federal agencies.
The goal is to make sure federal data is consistently protected at a high level in the cloud.
Getting FedRAMP authorization is serious business. The level of security required is mandated by law. There are 14 applicable laws and regulations, along with 19 standards and guidance documents. It’s one of the most rigorous software-as-a-service certifications in the world.
Our FedRAMP compliance is a reflection of our commitment to your data security.
Related Products
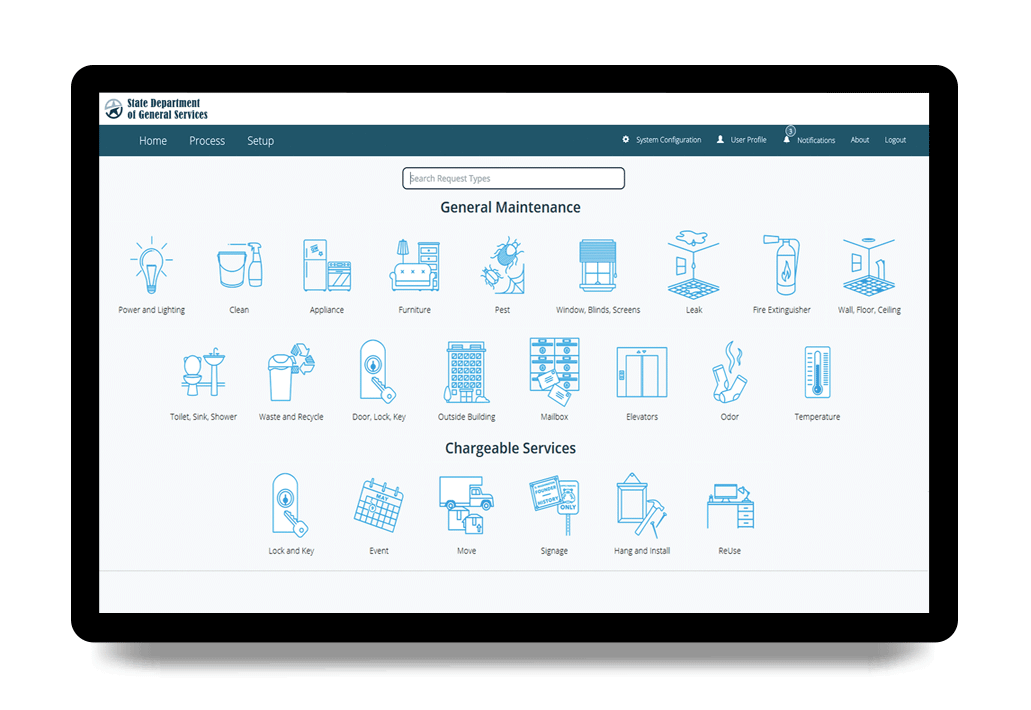
Engage
Engage is a family of self-service portal products that extend the power of FacilityForce to the community you serve, enhancing communication and improving customer service.
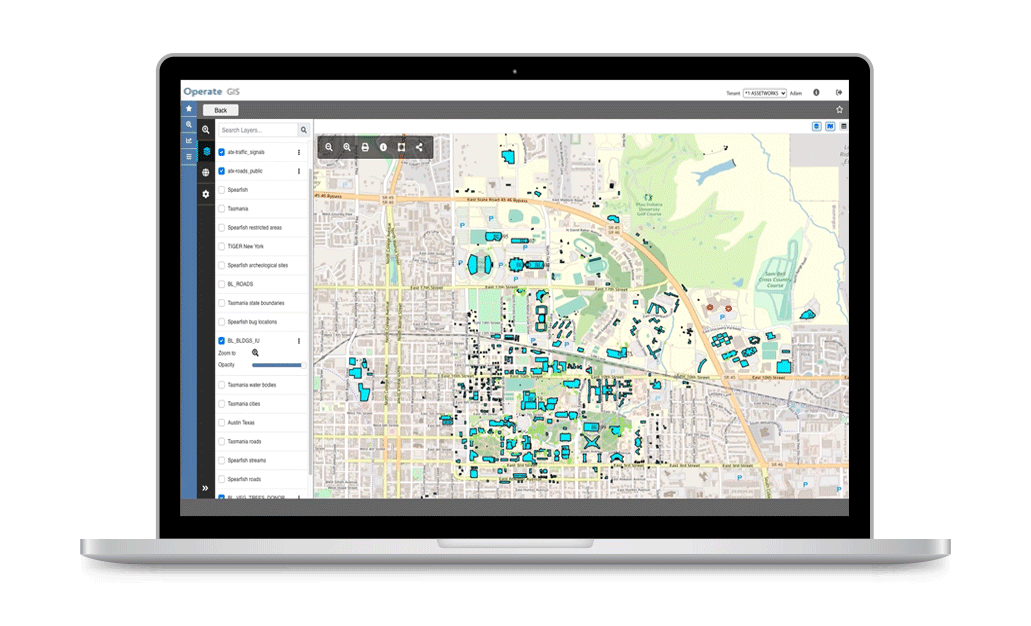
Locate
Locate enables map-centric asset management with the power of Esri's ArcGIS embedded in FacilityForce. Bring your data to life visually and work with assets, work orders and more on interactive maps.
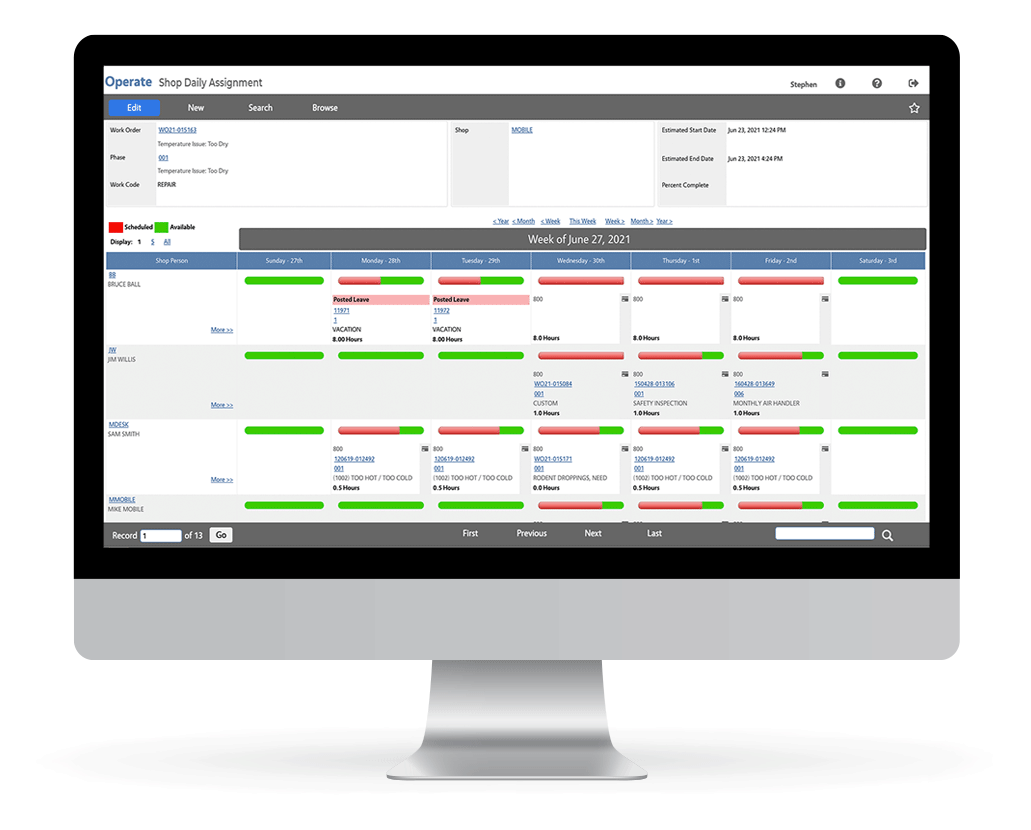
Operate
FacilityForce Operate is the core family of integrated enterprise solutions and specialized modules used to holistically manage facilities and assets, and to maximize their value to your organization.

Perform
Perform is a family of mobile applications that puts the power of FacilityForce in the hands of your field personnel and technicians, making them more productive on-the-go, wherever they need to be.

Analyze
Analyze is the business intelligence solution built into the FacilityForce platform, which makes valuable and actionable business insights available to stakeholders in your organization.

Automate
Automate is an optional add-on to the FacilityForce platform that provides for business process automation.
/Adobe%20Stock%20Images/AdobeStock_141661308.jpeg)
Integrate
Integrate is an optional add-on to the FacilityForce platform that focuses on exchanging data with other systems through standardized, configurable connections.
Testimonials

Thomas Miller - Chief Real Estate Officer

Tim Corbett - Chief Deputy Director

Anthony Griffin - Director of O&M
Related Learning

NASFA's 2026 National Conference & Expo
FacilityForce is honored to be a Platinum Sponsor of NASFA's 2026 National Conference. Taking place...
Keep reading
Wyoming’s Legacy of Stewardship: How Data is Powering Smarter, Stronger Schools
The Wyoming State Construction Department (SCD) oversees more than $5 billion in educational...
Keep readingLet's Chat
The best way to confirm whether our software is a good fit for your organization (and vice versa) is for us to discuss your specific challenges and goals, so let's chat...
